· Jesse Edwards · Case Studies
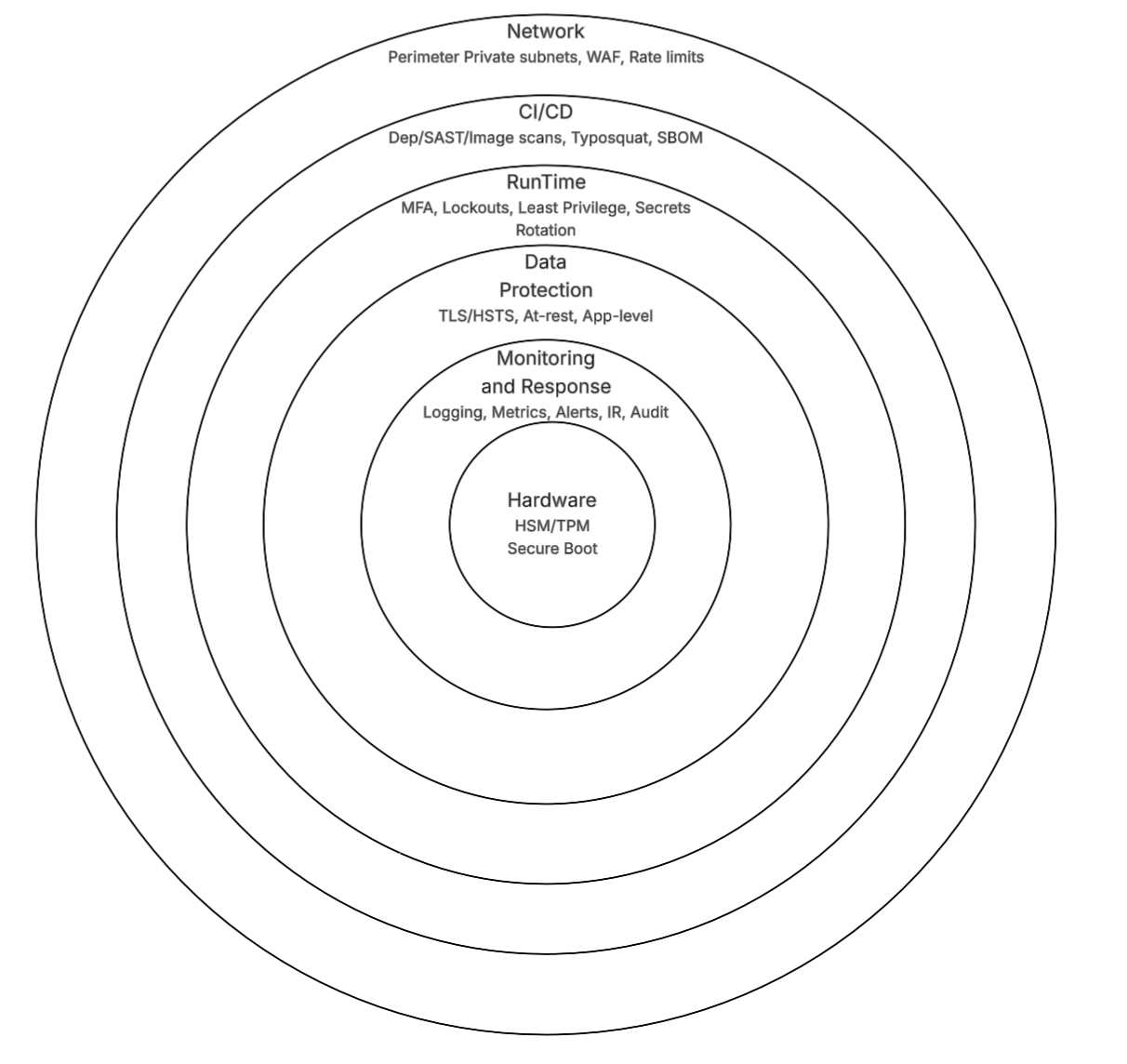
Layered Security, from Hardware to Runtime
Layered security from hardware to runtime: TPM/HSM, WAF, CI/CD scanning, secrets rotation, and encryption. Practical implementation beyond HTTPS.
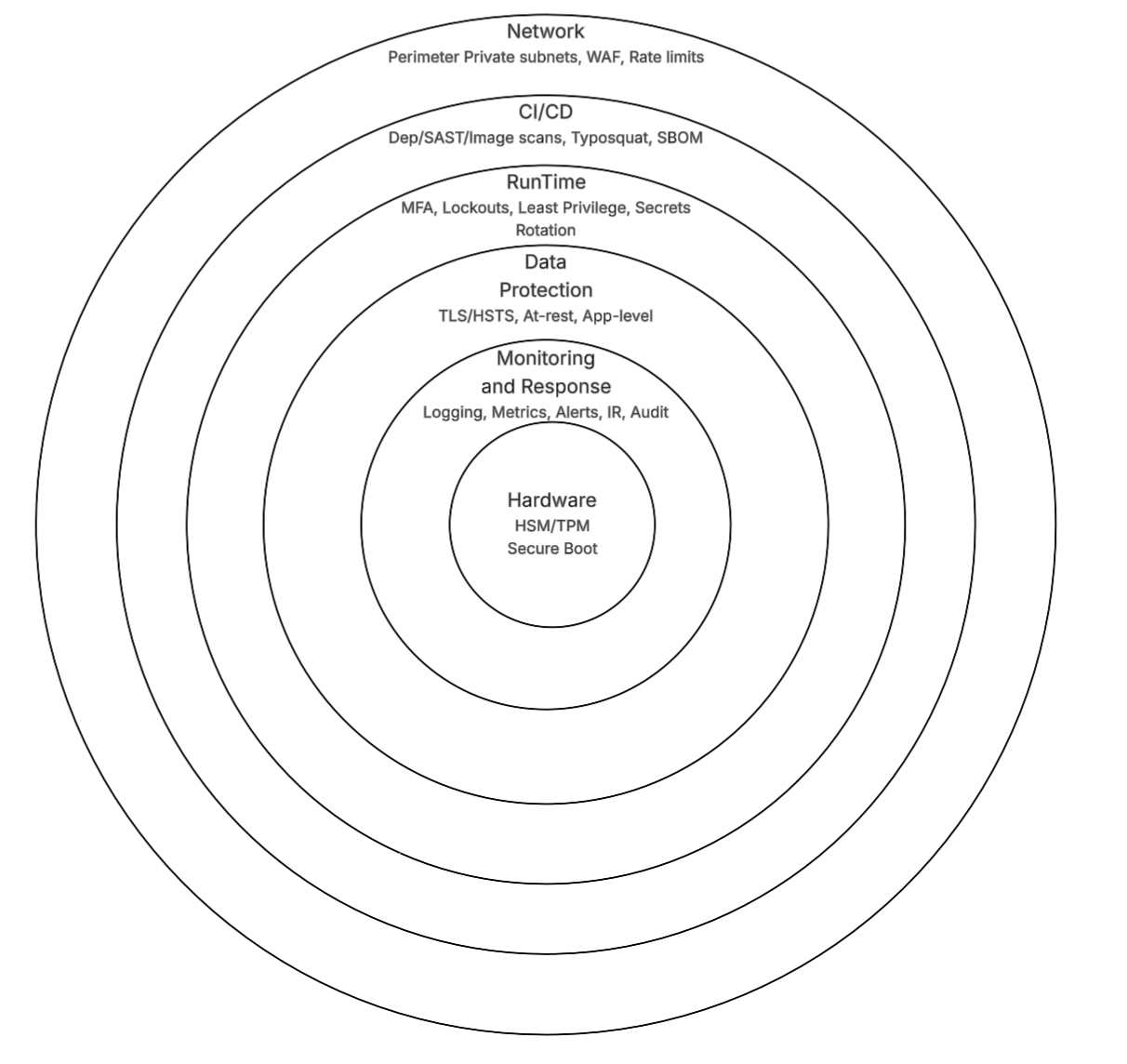
Layered security from hardware to runtime: TPM/HSM, WAF, CI/CD scanning, secrets rotation, and encryption. Practical implementation beyond HTTPS.
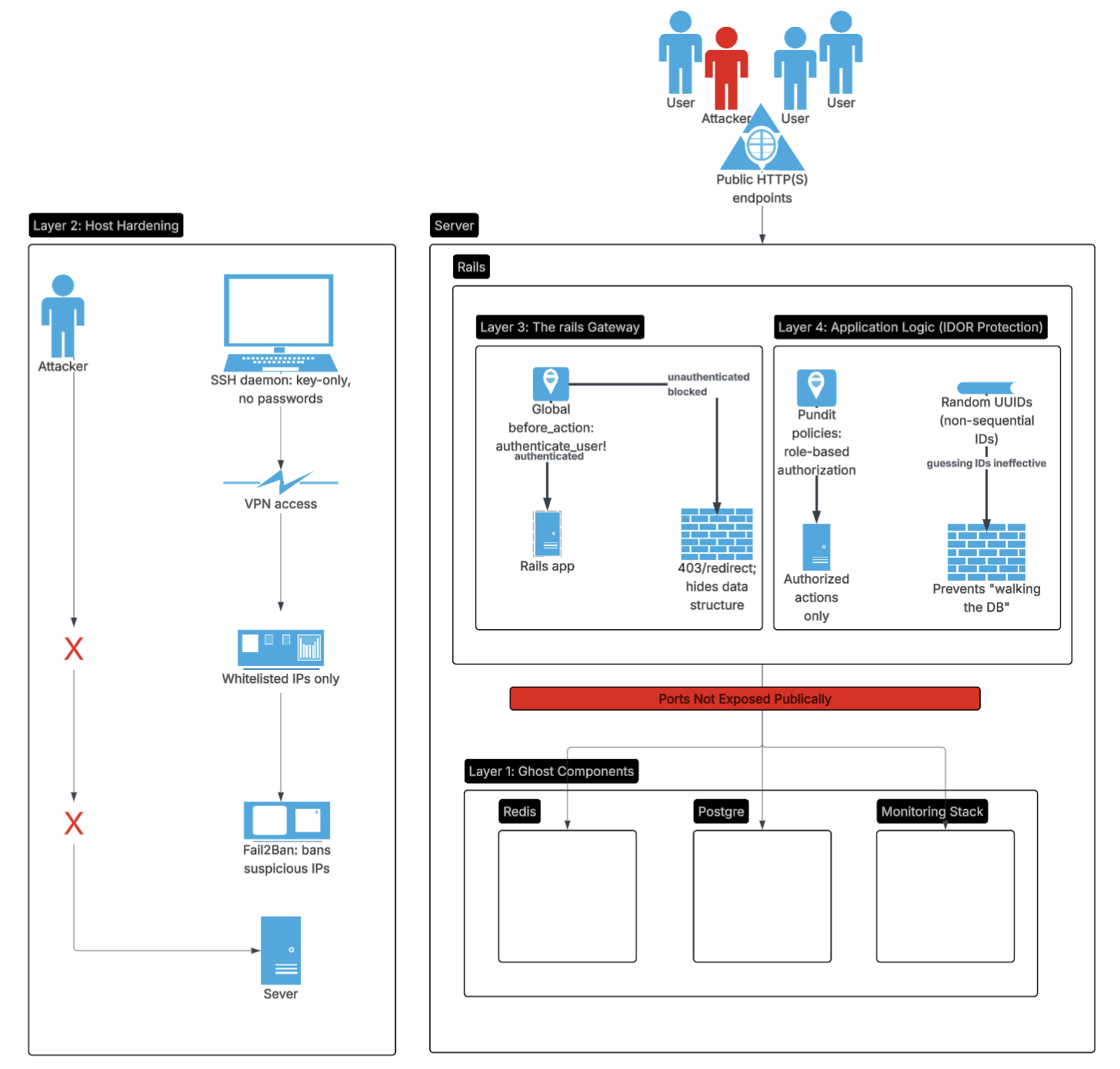
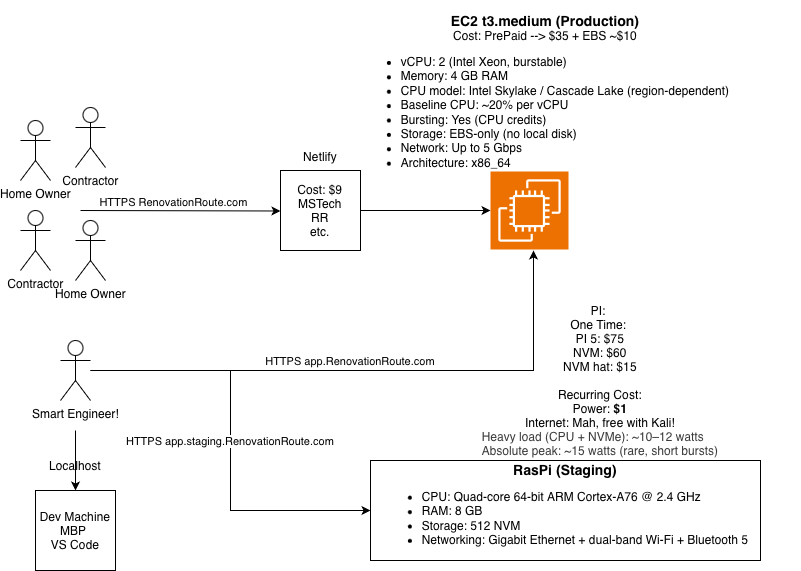
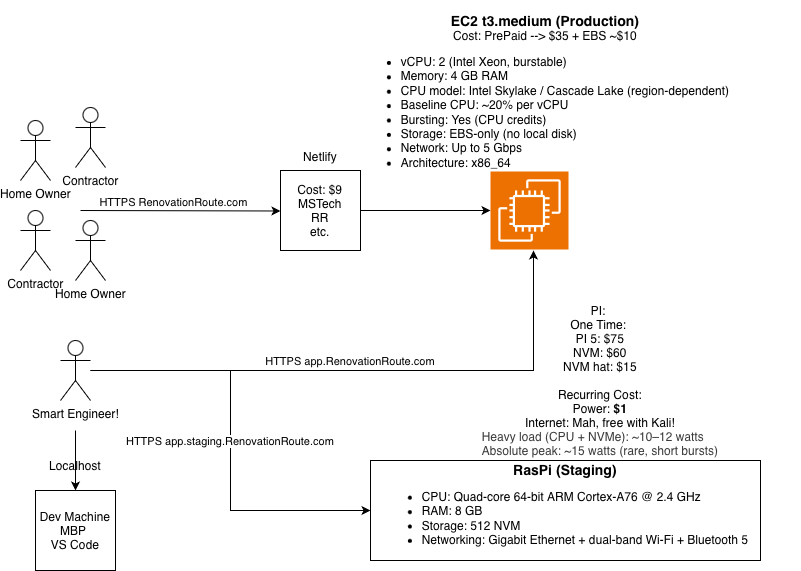
How to build professional grade security layers on a lean, single node stack using Rails and Kamal.
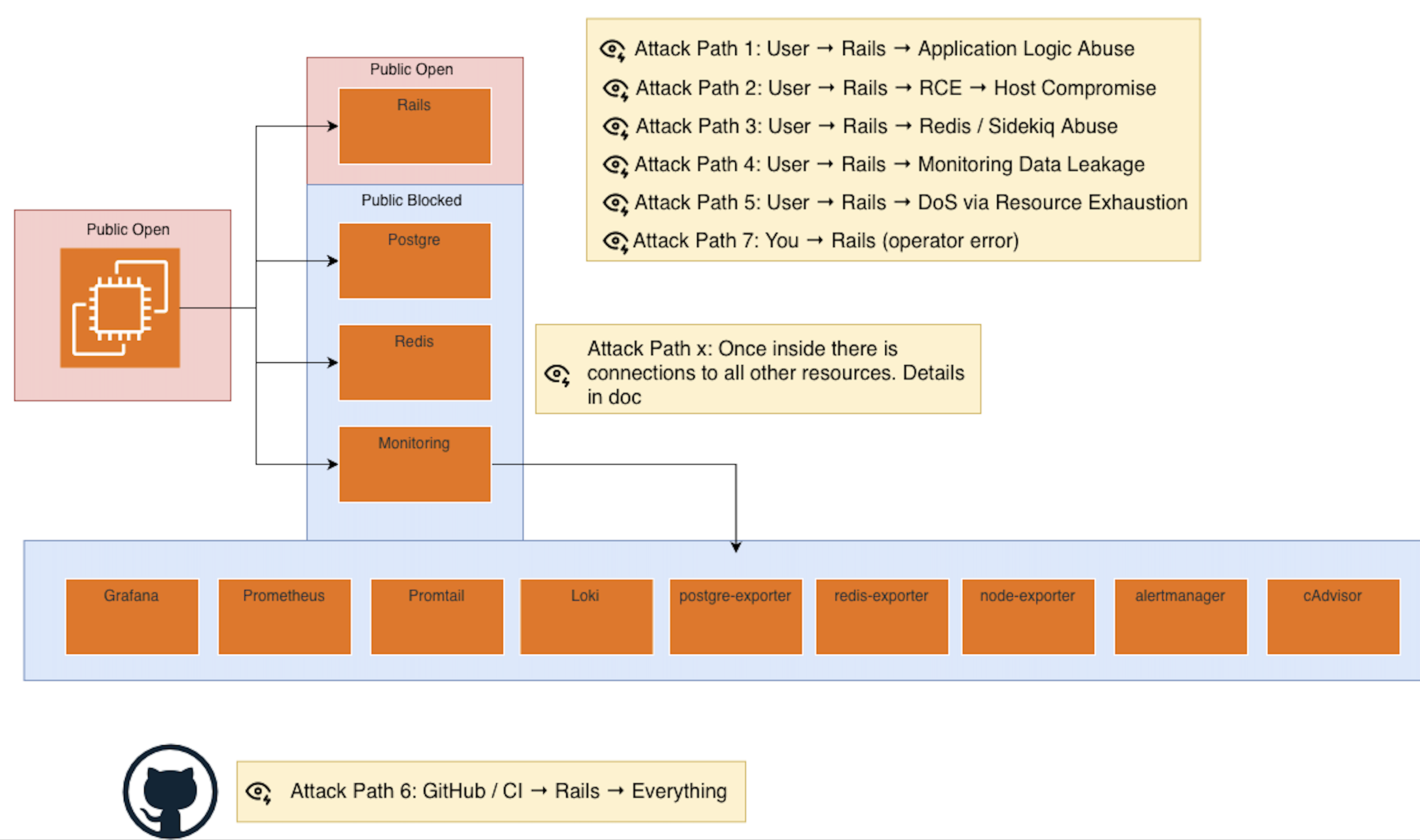
Security is not easy and that is why so many products get it wrong part 1.
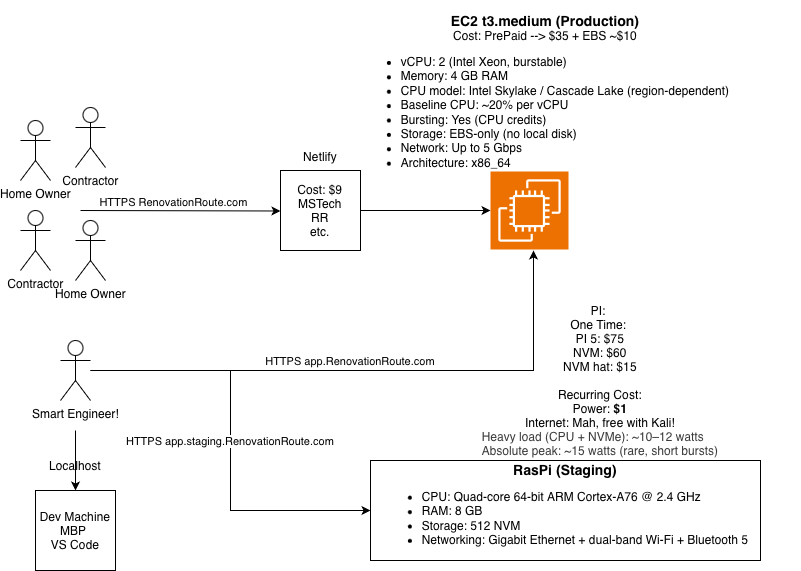
Here's why I chose restraint over hype and how to save money early on.
Mitigations for secrets handling, OAuth bypasses, dependency typosquatting, prompt injection, and more.
Security is hard. That’s why most products get it wrong.