· Jesse Edwards · Case Studies
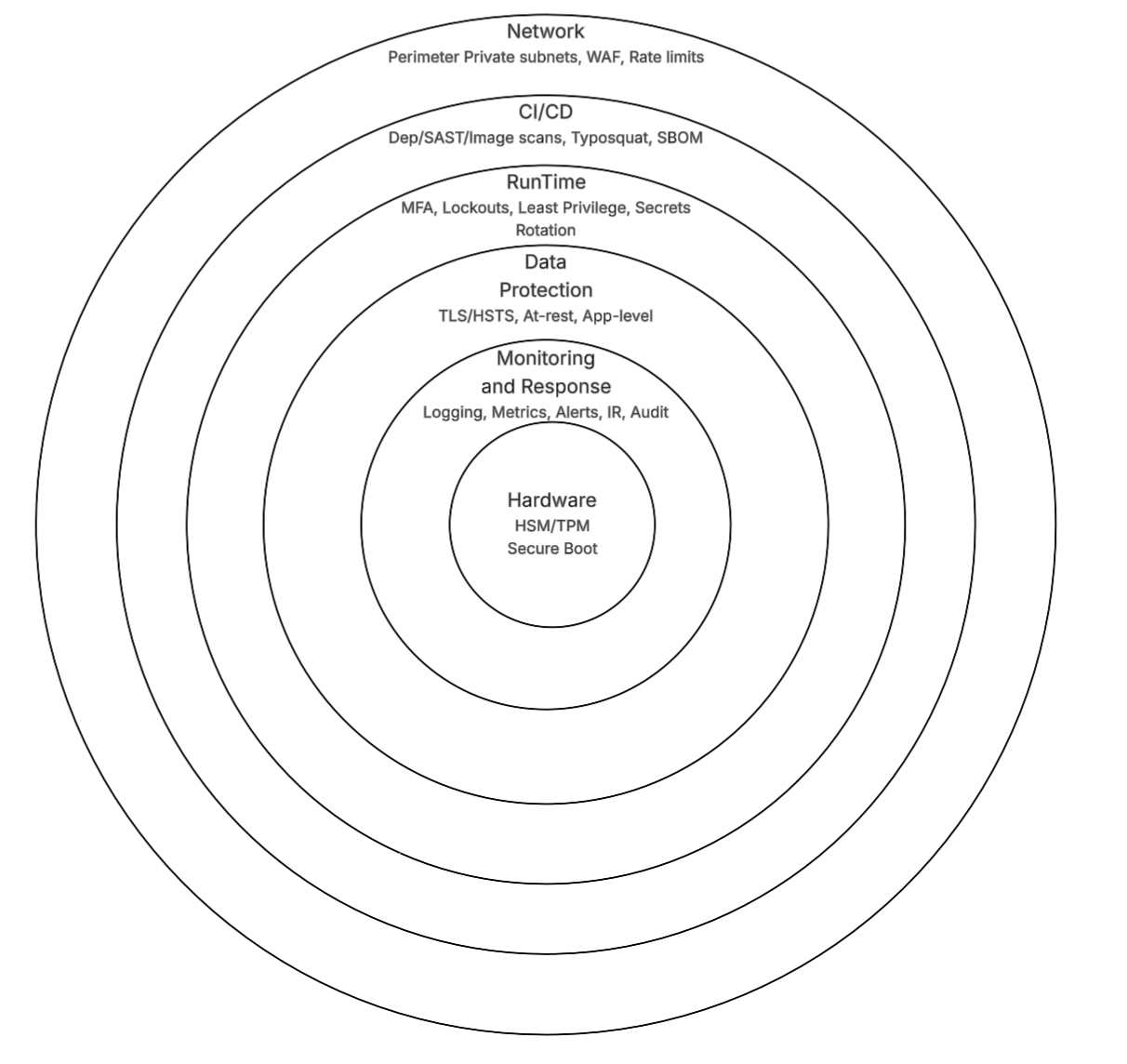
Layered Security, from Hardware to Runtime
Layered security from hardware to runtime: TPM/HSM, WAF, CI/CD scanning, secrets rotation, and encryption. Practical implementation beyond HTTPS.
Layered security from hardware to runtime: TPM/HSM, WAF, CI/CD scanning, secrets rotation, and encryption. Practical implementation beyond HTTPS.
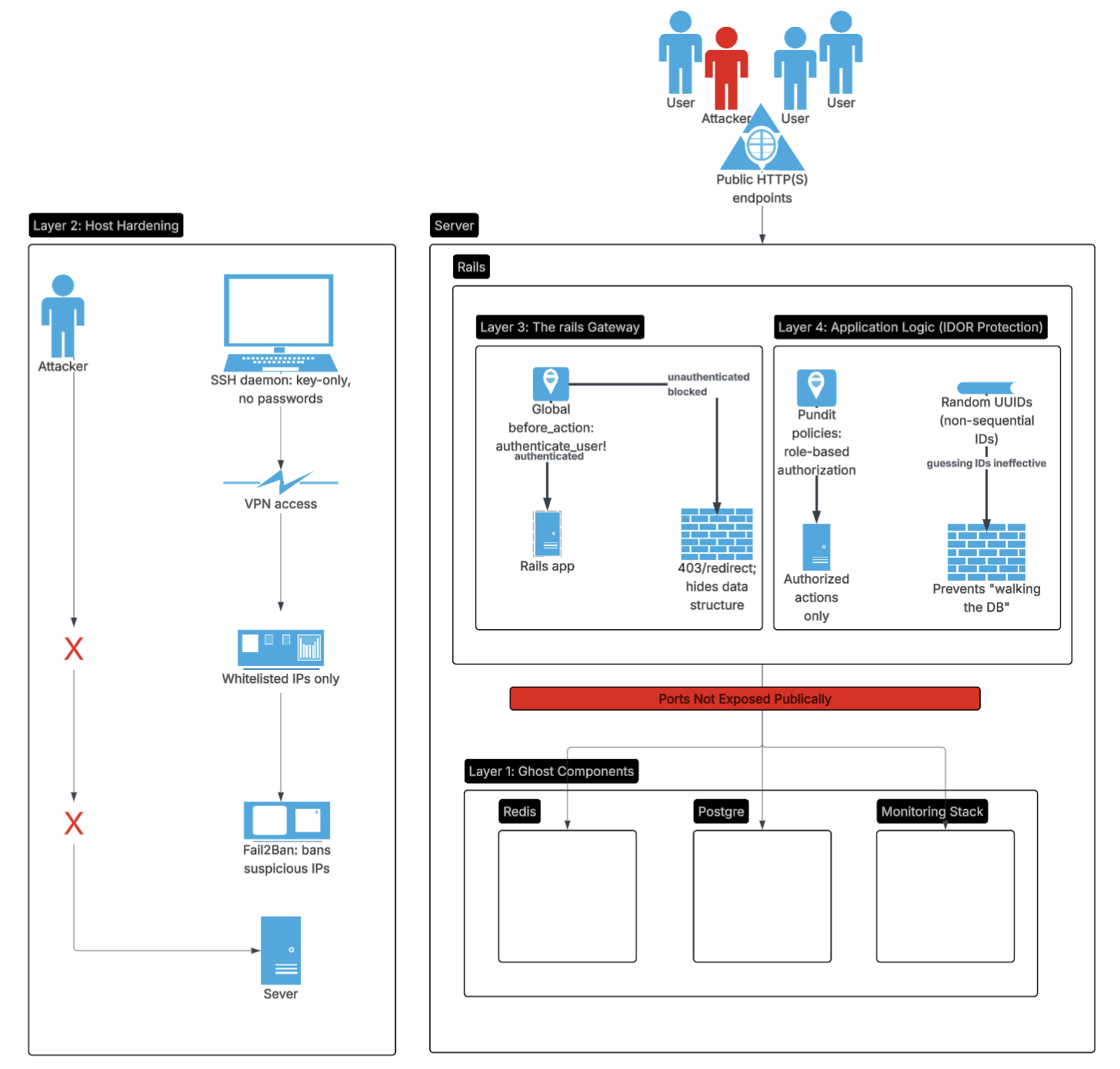
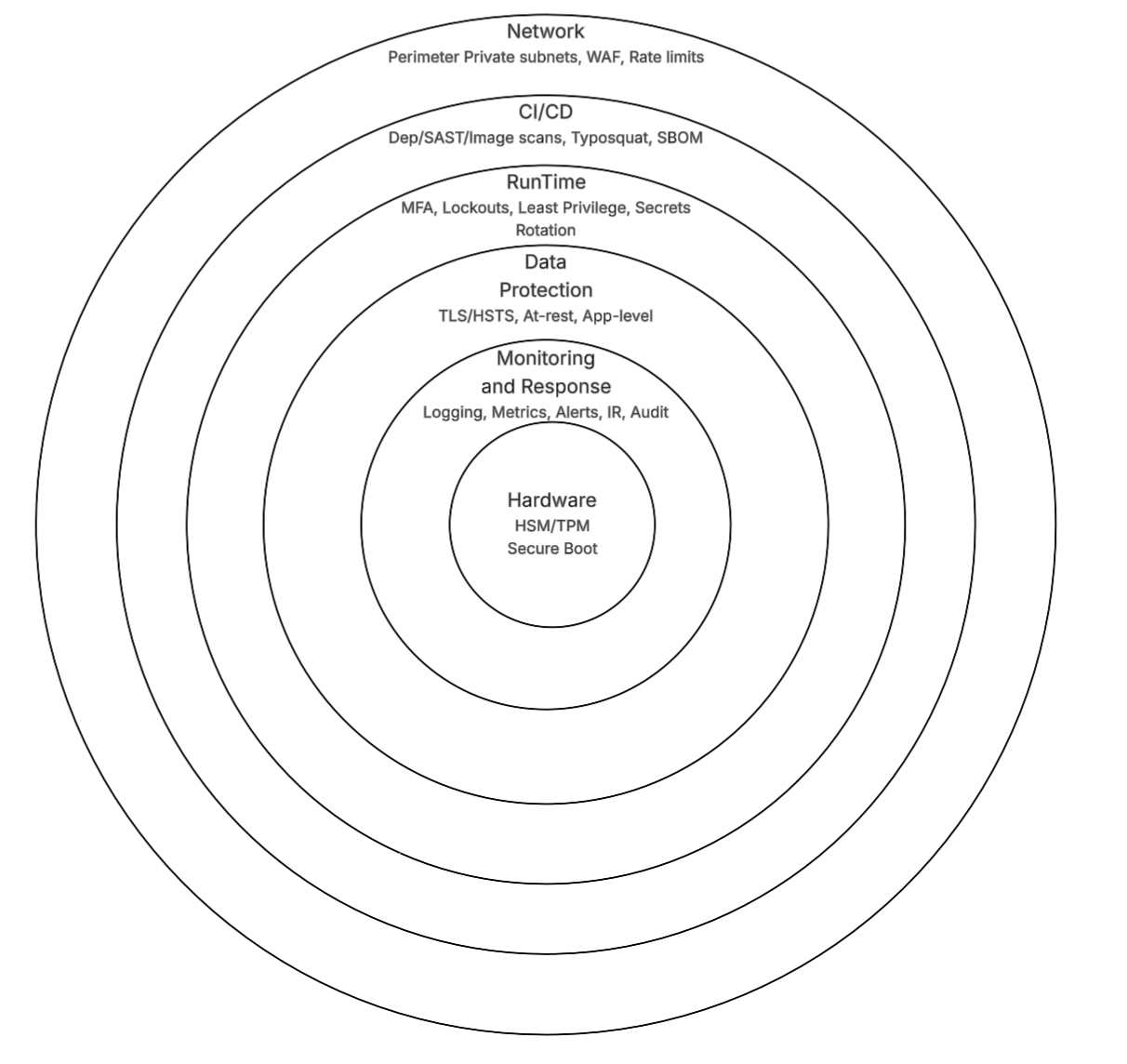
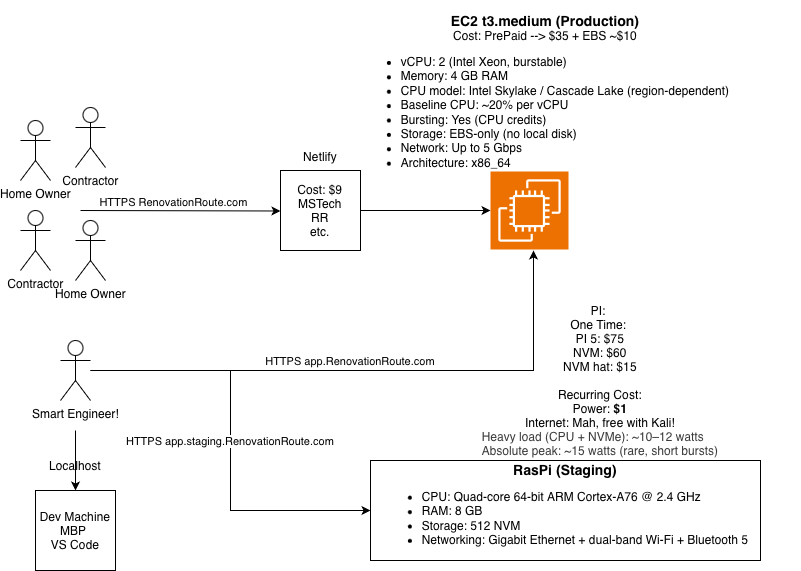
How to build professional grade security layers on a lean, single node stack using Rails and Kamal.
Mitigations for secrets handling, OAuth bypasses, dependency typosquatting, prompt injection, and more.
Security is hard. That’s why most products get it wrong.

Most construction software was not built by people who lived through the problems. RenovationRoute exists because the failures I kept seeing were not technology problems. They were architecture, process, and trust problems.