· Jesse Edwards · Case Studies
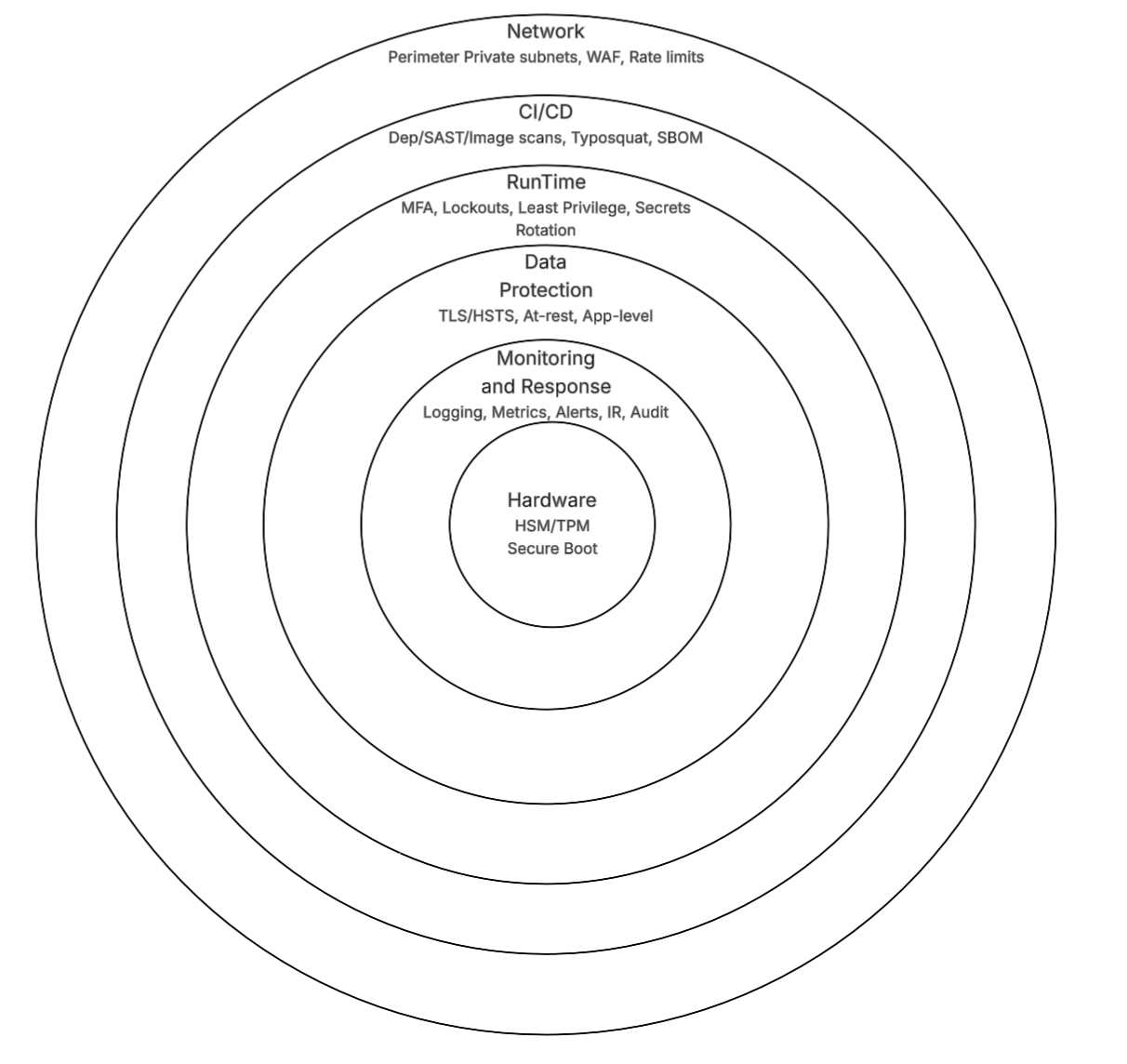
Layered Security, from Hardware to Runtime
Layered security from hardware to runtime: TPM/HSM, WAF, CI/CD scanning, secrets rotation, and encryption. Practical implementation beyond HTTPS.
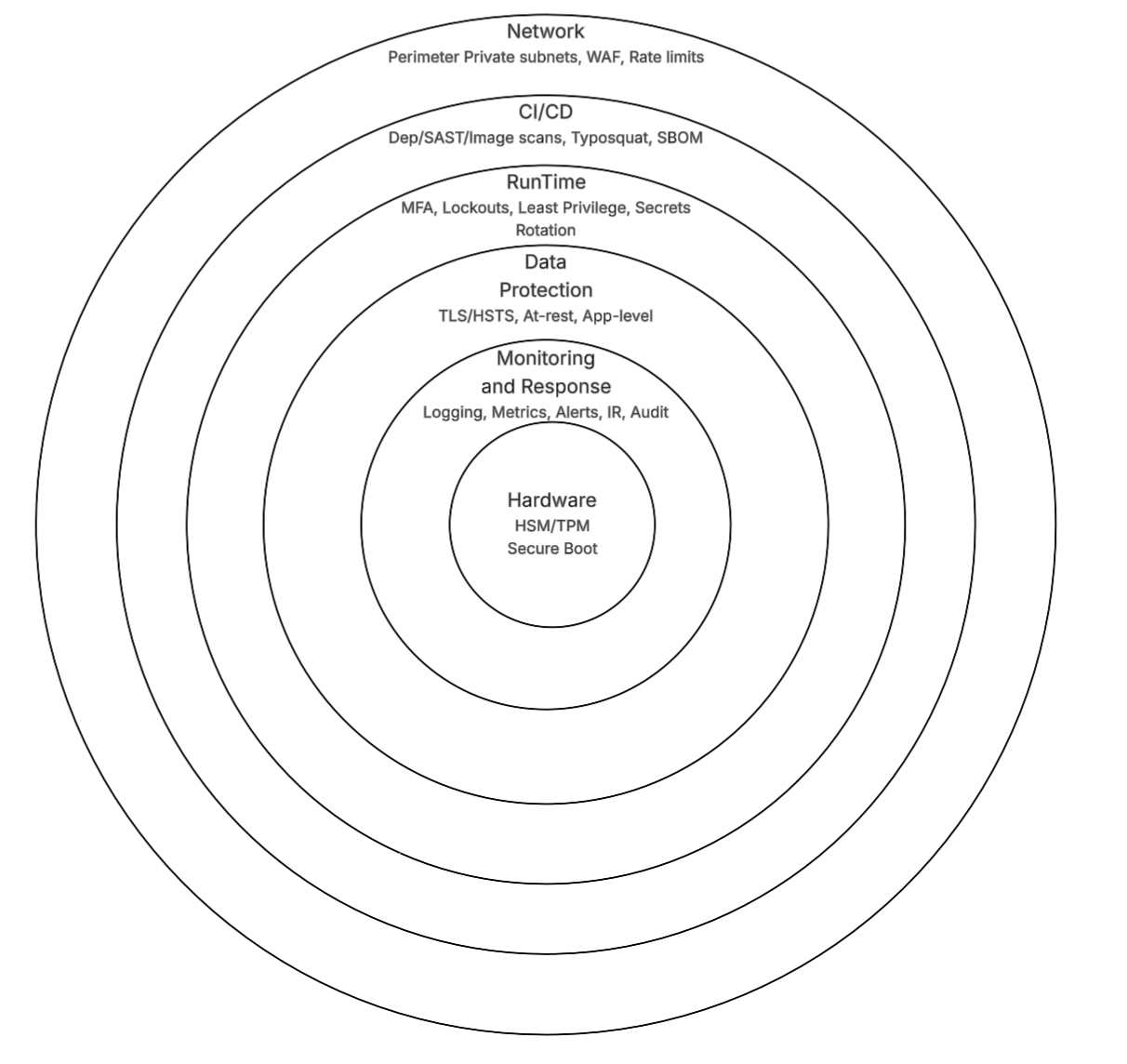
Layered security from hardware to runtime: TPM/HSM, WAF, CI/CD scanning, secrets rotation, and encryption. Practical implementation beyond HTTPS.